Operations
Plan and execute security operations — from AI-assisted red teaming to multiplayer CLI engagements.
What is an Operation?
An Operation is a coordinated sequence of security actions performed against a target. Operations can be investigative or offensive in nature, performed with or without initial access, and can contain multiple parallel streams of work. Use them for red team missions, adversary emulation exercises, training, or live investigation of your environments.
Method provides two ways to run Operations: Operator (a visual workspace) and Overwatch (a CLI for local tooling). Both can be accessed from within the Reaper application in the sidebar.
Operator
Operator is the primary workspace for running Operations. It serves as an IDE for Security Engineering and Offensive Engineering workflows, with Tools, Ontology data, and AI at your fingertips.
The workspace
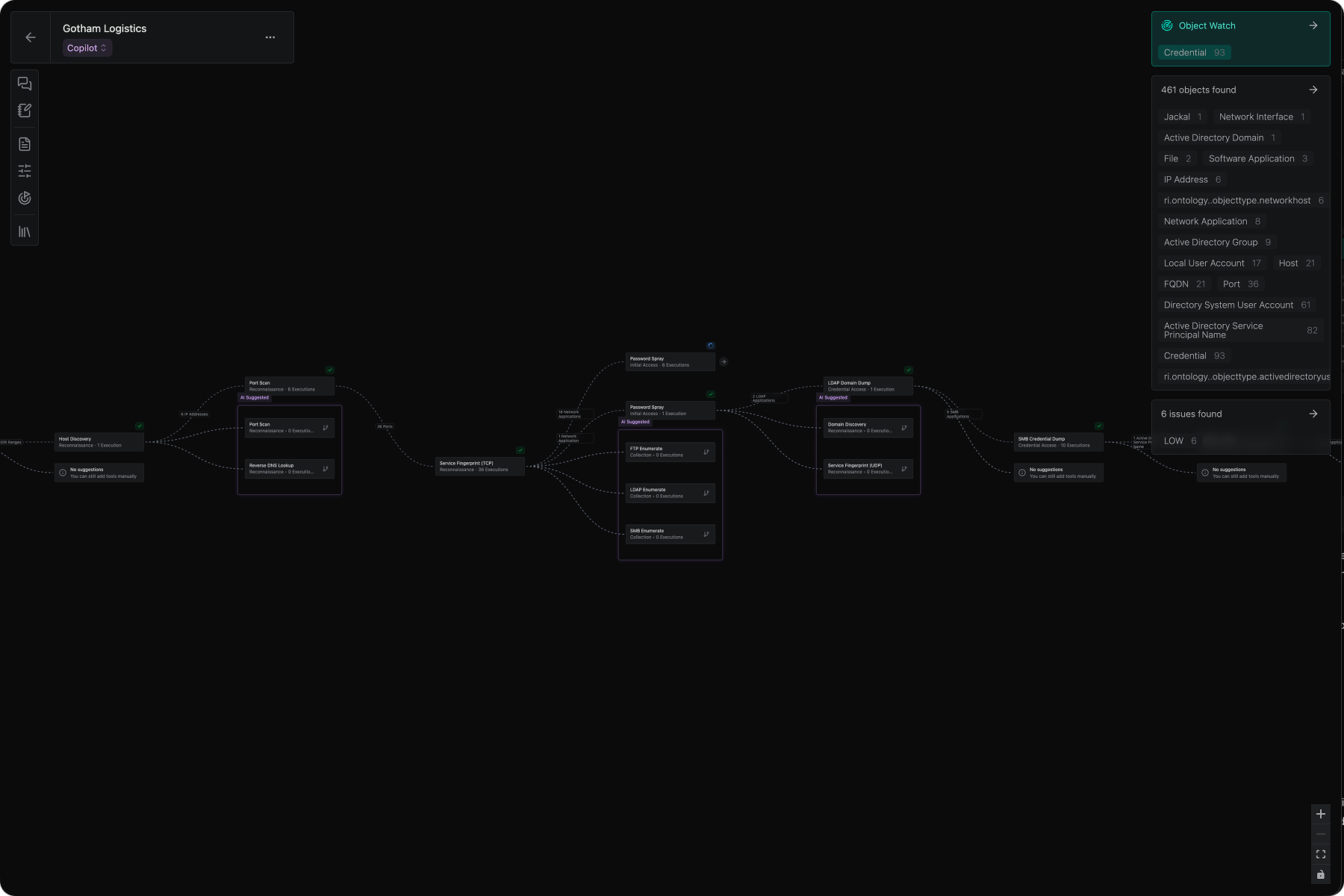
The Operator workspace is built around a central graph canvas:
- Left panel: Contains AI chat, Operation objectives, Rules of Engagement, adversary intelligence, and the complete Tool Library
- Central graph: Visualizes the steps taken in your operation. Nodes represent Tool executions; edges show data types flowing between them. For Operations in a target network (not the open web), switch tabs to see a Network Map of the target network.
- Right panel: Objects and Issues discovered. Select a node to filter to that step’s findings, or deselect to see the full operation lineage
Operating modes
Operator offers three modes:
- Manual mode: Fully operator-driven. No AI suggestions for tool executions, but you can still use chat with AI for questions and analysis.
- Co-pilot mode: Human-in-the-loop, AI-assisted operation. You receive AI-suggested tool recommendations based on the mission objective, recent findings, environmental context, and adversary intelligence. Accept or decline each recommendation before execution.
- Auto mode: The system runs completely autonomously within pre-defined guardrails set by the operator.
You can learn more about Co-pilot and Full Auto mode in Operator AI.
Adversary emulation
Operations can include Adversaries, created from uploaded adversary intelligence, to power AI-driven adversary emulation. When an Adversary is selected, Operator AI suggestions reflect how that adversary would behave against your targets. You can chat with the Operation AI to learn about how the adversary would think about your targets.
Rules of Engagement
Operations support configurable guardrails: No Strike lists, restricted tool executions, and operational risk controls that enforce safety boundaries during execution.
Object Watch
Declare specific Object Types of interest; the system passively monitors for them and alerts you when they are discovered during an operation.
Method Tools
Operator leverages Method’s full suite of tools. You can explore them in the Tool Library, in the left panel. As you progress through your operation, only the tools that are applicable to the data you have discovered are suggested.
For a step-by-step walkthrough for using Operator, see Run your first Operation.
Overwatch
Overwatch is a cross-platform CLI for running operations locally using your own tools, while integrating with the full Method platform.
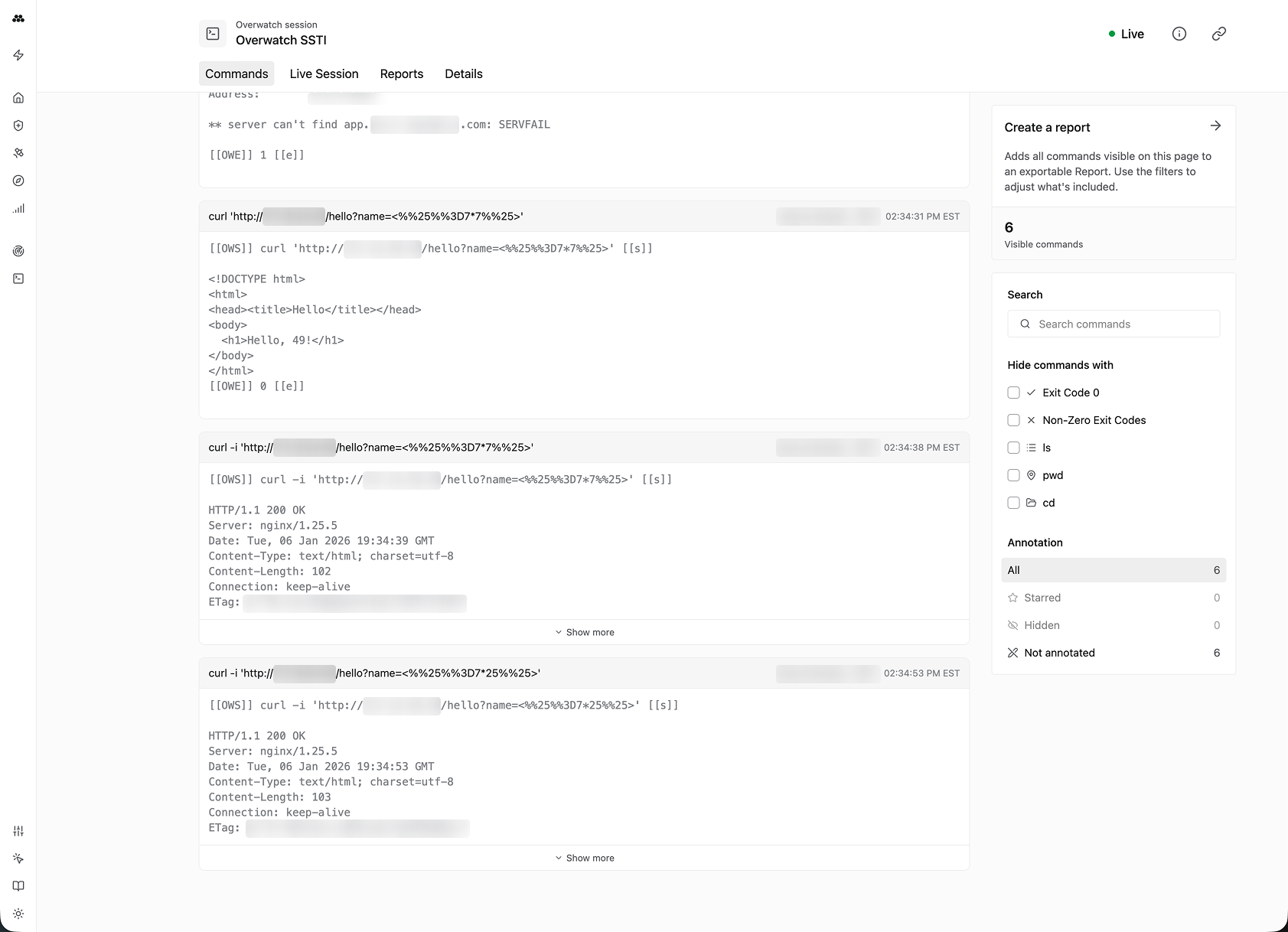
Session recording
Overwatch records all commands entered, their outputs, and relevant metadata. Terminal session recording is modeled after tools like asciinema, enabling accurate playback and review.
Collaboration
Multiple operators can join the same Overwatch session from their respective terminals. Overwatch tracks each operator’s commands and funnels them into a single session for unified tracking and reporting.
Report generation
Use Overwatch’s terminal history to filter or curate command logs, then generate a Report with a single click.